Ransomware is affecting organizations at an increasing rate. According to the recent 1H Global Threat Landscape Report from FortiGuard Labs, ransomware incidents have increased nearly 1100% over the past twelve months. The latest global ransomware survey by Fortinet reports that 67% of organizations report being a ransomware target, with nearly half of that reporting being attacked more than once, and almost one in six reporting being attacked three or more times.
As a result, 94% of organizations report that they are concerned about ransomware attacks, with 76% reporting that they are very concerned. 85% of respondents are more concerned about ransomware attacks than any other cyberattack. They are most concerned about data loss (62%) in this regard. Businesses today rely on data. Although the loss of productivity (38%) and interruption of operations (36%) are also top concerns, they can be easily recovered compared to a significant loss of data. Recent high-profile attacks such as the Colonial Pipeline incident that disrupted oil and gasoline distribution on the East Coast of the United States and the JBS Foods incident that sparked concerns about a global meat shortage have reinforced these concerns.
Ransomware Attacks
The risks of ransomware are well known to organizations. As a result, they have had plenty of time to prepare. Over 96% of those surveyed felt they were moderately prepared for an attack. They may feel prepared, but their tools and plans to deal with an attack seem disconnected. Less than half of the respondents have implemented strategies that include network segmentation (48%), forensics (34%), testing ransomware recovery methods (28%), or red team/blue team exercises (13%). They also place critical security technologies, like secure email gateways (33%), network segmentation (31%), UEBA (user and entity behavior analytics) (30%), SD-WAN (13%), and sandboxing (7%) at the bottom of their list of tools they consider essential for securing themselves against ransomware.
Essential to Secure Against Ransomware
Instead, they rely on employee cyber training (61%), offline backups (58%), and cybersecurity/ransomware insurance (57%). Such measures are more positive, but not complete. Interestingly, 72% of respondents said they had a ransom policy in place, but only 49% said they paid the ransom in full. In another 25% of cases, the decision to pay a ransom depends on its price.
Protect Your Organization Against Ransomware Attacks with Fortinet
Know Your Risks and Plan Accordingly:
Ransomware attacks use several different strategies, and organizations must be prepared for them. Using a Secure Web Gateway can help end-users protect their systems from web-based attacks that target and compromise vulnerable systems. The good news is that 52% of organizations plan to use this technology. However, the most common entry method reported by respondents was phishing, a type of attack that combines social engineering, user manipulation, and a malicious email with malicious links. The modern secure email gateway should detect malicious links and attachments, analyze them in a sandbox, and ideally disarm them before they exploit a user to download ransomware or browse to links or files in a high-security browser environment.
Stop Known Threats:
It is also important for companies to find a cybersecurity solution that can stop all known ransomware threats. To achieve this security must be layered(layered security model), incorporating network, endpoint, and data center controls that are powered by proactive global threat intelligence. In addition to traditional security tools, behavioral analytics can be used to detect and stop a breach quickly.
Detect New Threats:
Ransomware is constantly evolving and new variants are being released; therefore, it is essential to use sandboxing and advanced detection techniques to detect new variants across these same vectors. Additionally, real-time behavioral detection at the endpoint is just as critical as seeing malware before it gets there.
Protect Endpoints:
In addition to advanced endpoint technologies like EDR (endpoint detection and response), organizations must implement key technologies like Secure Web Gateways, SASE, and ZTNA for secure application access to extend business protections to their remote and mobile workers.
Prepare for the Unexpected:
Ransomware’s worm-like behavior can be mitigated by dynamic network segmentation. With an effective segmentation strategy in place, breaches can be limited to a relatively small portion of a network. It is also vital to back up data offline and to have the ability to recover it.
Encryption is Critical:
Encrypting all data at rest can be time-consuming, but it prevents criminals from threatening to expose data online or resell stolen information on the dark web if a ransom is not paid.
Secure the Entire Infrastructure:
The SD-WAN technology is rapidly replacing traditional WAN connections as it is smarter and more agile. But for many organizations, SD-WAN is not a better approach to ensuring data security-which is why a secure SD-WAN solution should be considered initially as the primary solution to replace legacy remote connectivity to cloud and data center resources from branches and certain super-users.
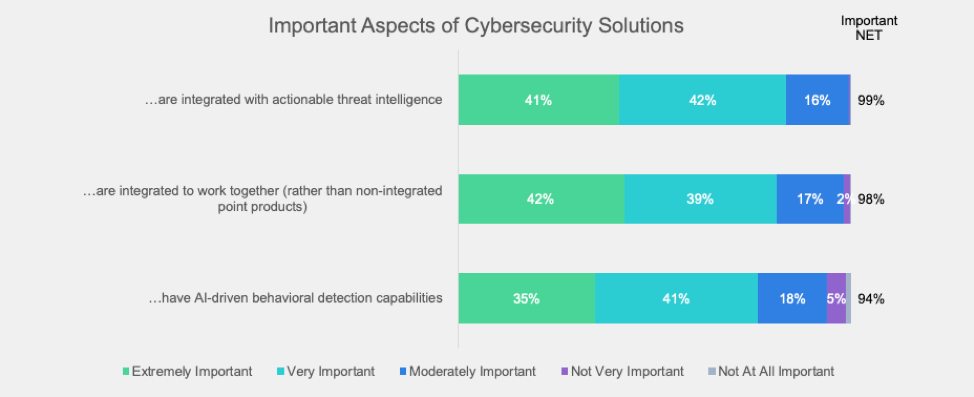
Important Aspects of Cybersecurity Solutions
Ransomware is a global problem
Ransomware is a major concern around the world. The White House recently announced the formation of a cybersecurity task force. The law has also designated those who perpetrate ransomware attacks as terrorists, giving law enforcement agencies additional resources and stronger penalties for fighting cybercriminals. Several countries have also taken similar measures. Similarly, law enforcement agencies, like Interpol, are raising the bar on ransomware prevention. Additionally, the Department of Justice has directed federal prosecutors across the country to coordinate any ransomware investigations with the newly formed Ransomware and Digital Extortion Task Force.
We all need to do our part. Starting with developing an effective ransomware strategy, including advanced security resources for dealing with ransomware attack vectors. This is something every company must do.